Stakpak Agent
STDIODevOps AI agent with Terraform, container building, and cloud security analysis capabilities
DevOps AI agent with Terraform, container building, and cloud security analysis capabilities
You can't trust most AI agents with your DevOps. One mistake, and your production is toast. Stakpak is built different:
Generate infrastructure code, debug Kubernetes, configure CI/CD, automate deployments, without giving an LLM the keys to production.
--enable-subagents flag)brew tap stakpak/stakpak brew install stakpak
To update it you can use
brew update brew upgrade stakpak
Download the latest binary for your platform from our GitHub Releases.
This image includes the most popular CLI tools the agent might need for everyday DevOps tasks like docker, kubectl, aws cli, gcloud, azure cli, and more.
docker pull ghcr.io/stakpak/agent:latest
You can use your own Anthropic or OpenAI API keys, custom OpenAI compatible endpoint, or a Stakpak API key.
Just run stakpak and follow the instructions which will create a new API key for you.
stakpak
Brave users may encounter issues with automatic redirects to localhost ports during the API key creation flow. If this happens to you:
Copy your new key from the browser paste it in your terminal
STAKPAK_API_KEYexport STAKPAK_API_KEY=<mykey>
~/.stakpak/config.tomlstakpak login --api-key $STAKPAK_API_KEY
stakpak account
Create ~/.stakpak/config.toml with one of these configurations:
Option 1: Bring Your Own Keys (BYOK) - Use your Anthropic/OpenAI API keys:
[profiles.byok] provider = "local" # customize models smart_model = "claude-sonnet-4-5" eco_model = "claude-haiku-4-5" [profiles.byok.anthropic] api_key = "sk-ant-..." [profiles.byok.openai] api_key = "sk-..." [settings]
Option 2: Bring Your Own LLM - Point to a local OpenAI-compatible endpoint (e.g. LM Studio):
[profiles.offline] provider = "local" smart_model = "qwen/qwen3-coder-30b" eco_model = "qwen/qwen3-coder-30b" [profiles.offline.openai] api_endpoint = "http://127.0.0.1:1234/v1/chat/completions" api_key = "" [settings]
Then run with your profile:
stakpak --profile byok # or stakpak --profile offline
# Open the TUI stakpak # Resume execution from a checkpoint stakpak -c <checkpoint-id>
docker run -it --entrypoint stakpak ghcr.io/stakpak/agent:latest # for containerization tasks (you need to mount the Docker socket) docker run -it \ -v "/var/run/docker.sock":"/var/run/docker.sock" \ -v "{your app path}":"/agent/" \ --entrypoint stakpak ghcr.io/stakpak/agent:latest
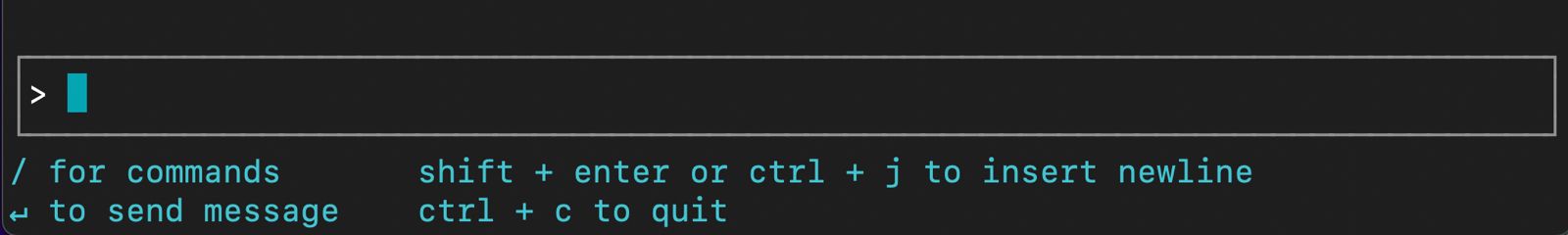
Arrow keys or Tab to select optionsEsc to exit the prompt? for Shortcuts/ for commands↵ to send messageShift + Enter or Ctrl + J to insert newlineCtrl + C to quitYou can use Stakpak as a secure MCP proxy or expose its security-hardened tools through an MCP server.
--tool-mode local) - File operations and command execution only (no API key required)--tool-mode remote) - AI-powered code generation and search tools (API key required)--tool-mode combined) - Both local and remote tools (default, API key required)# Local tools only (no API key required, mTLS enabled by default) stakpak mcp start --tool-mode local # Remote tools only (AI tools optimized for DevOps) stakpak mcp start --tool-mode remote # Combined mode (default - all tools with full security) stakpak mcp start # Disable mTLS (NOT recommended for production) stakpak mcp start --disable-mcp-mtls
Additional flags for the MCP server:
--disable-secret-redaction – not recommended; prints secrets in plaintext to the console--privacy-mode – redacts additional private data like IP addresses and AWS account IDs--enable-slack-tools – enables experimental Slack toolsStakpak also includes an MCP proxy server that can multiplex connections to multiple upstream MCP servers using a configuration file.
# Start MCP proxy with automatic config discovery stakpak mcp proxy # Start MCP proxy with explicit config file stakpak mcp proxy --config-file ~/.stakpak/mcp.toml # Disable secret redaction (NOT recommended – secrets will be printed in logs) stakpak mcp proxy --disable-secret-redaction # Enable privacy mode to redact IPs, account IDs, etc. stakpak mcp proxy --privacy-mode
ACP is a standardized protocol that enables AI agents to integrate directly with code editors like Zed, providing seamless AI-powered development assistance.
~/.config/zed/settings.json:{ "agent_servers": { "Stakpak": { "command": "stakpak", "args": ["acp"], "env": {} } } }
stakpak acp
+ → New stakpak threadManage your standard operating procedures (SOPs), playbooks, and runbooks with Stakpak Rulebooks. Rulebooks customize agent behavior and provide context-specific guidance.
# List all rulebooks stakpak rulebooks get # or use the short alias stakpak rb get # Get a specific rulebook stakpak rb get stakpak://my-org/deployment-guide.md # Create or update a rulebook from a markdown file stakpak rb apply my-rulebook.md # Delete a rulebook stakpak rb delete stakpak://my-org/old-guide.md
Rulebooks are markdown files with YAML frontmatter:
--- uri: stakpak://my-org/deployment-guide.md description: Standard deployment procedures for production tags: - deployment - production - sop --- # Deployment Guide Your deployment procedures and guidelines here...
Comprehensive testing report for Windows CLI functionality, including installation, configuration, and integration with WSL2 and Docker.
If our Agent saves you time or makes your DevOps life easier,
consider giving us a star on GitHub — it really helps!
